Google Says a Quantum Computer Could Crack Bitcoin in 9 Minutes. Here Is What That Means.
Last week, Google published research showing that a quantum computer could crack Bitcoin’s encryption in under nine minutes. Bitcoin’s average block confirmation time is ten minutes. That is not a coincidence. It is a race, and Bitcoin is currently losing.
The Short Answer
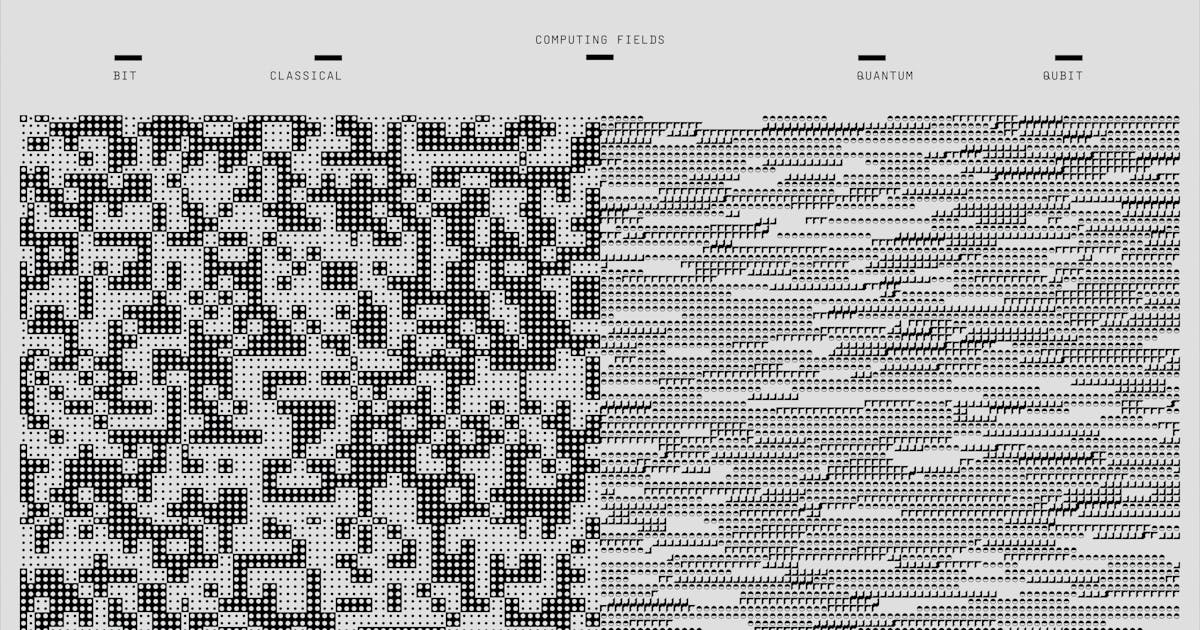
Bitcoin’s security rests on a mathematical problem that normal computers cannot solve in any reasonable timeframe. A quantum computer, which processes information in a fundamentally different way, can solve that same problem dramatically faster. Google’s March 2026 research estimates the required hardware has dropped from roughly 9 million quantum processors to fewer than 500,000. That is a 20-fold reduction in the barrier to breaking Bitcoin. The hardware still does not exist at that scale. But analysts now believe it could by 2029.
How Does Bitcoin’s Security Actually Work?
When you create a Bitcoin wallet, two things are generated: a private key (your secret) and a public key (your identity on the blockchain). Spending bitcoin requires proving you own the private key without actually revealing it, using a cryptographic signature. Today’s computers would take billions of years to reverse-engineer a private key from its public key. That is why Bitcoin is considered secure.
Quantum computers change this because they can run Shor’s algorithm, a method that turns that billions-of-years problem into a minutes-long one. The moment a quantum computer is powerful enough, anyone who can see your public key can steal your coins.
Two Ways Your Bitcoin Could Be at Risk
Why This Is Different From Previous Warnings
Quantum threats to Bitcoin are not new. What is new is the pace of progress. Three research papers published between May 2025 and March 2026 reduced the required qubit count by roughly 20x each time. The most recent Google paper was co-authored by a researcher from the Ethereum Foundation and a cryptographer from Stanford. It was sensitive enough that Google chose not to publish the actual attack circuits, releasing only a mathematical proof that the circuits work. That is an unusual step in academic research, and it signals the team considered the findings serious enough to require caution.
What Is Bitcoin Doing About It?
Developers have proposed several upgrades, none of which are active yet:
- BIP 360 would stop new addresses from publishing public keys on-chain. This protects future transactions but does nothing for coins already exposed.
- Post-quantum signatures using a NIST-approved standard called SLH-DSA would replace Bitcoin’s existing signature method. The tradeoff: signatures would grow from 64 bytes to over 8 kilobytes, which would meaningfully increase transaction fees.
- A commit/reveal scheme proposed by Lightning Network co-creator Tadge Dryja would protect transactions in the waiting room by pre-registering a fingerprint on-chain before broadcasting the full transaction. A thief forging a transaction after the fact would have no matching fingerprint, and the network would reject it.
- Hourglass V2 targets the 1.7 million already-exposed coins by limiting their spending to 1 BTC per block. It would not stop a quantum attacker from stealing them, but it would prevent a single overnight event from flooding the market and collapsing the price.